 |
| “Communication flow in the TDS 4.2 protocol” [msdn] |
Our recent PyConZA talk had several examples of why Python is often an easy choice of language for us to quickly try things out. One example came from looking at network traffic of a client authenticating with Microsoft SQL Server (in order to simulate the server later). By default, we can’t see what the authentication protocol looks like on the wire because the traffic is encrypted. This post is a brief account of stripping that encryption with a little help from Python’s Twisted framework.
The clean
overview of the authentication protocol on MSDN suggests that it would as easily readable as its diagram. Our first packet captures weren’t as enlightening. Only the initial connection request messages from the client and server were readable. Viewing the traffic in Wireshark showed several further messages without a hint that the payloads were encrypted. A clearer hint was in the
MSDN description of the initial client and server messages. There’s a byte field in the header called
ENCRYPTION. By default, both the client and server’s byte is set to
ENCRYPT_OFF(0x00), which actually means encryption
is supported but just turned off. Once both endpoints are aware that the other supports the encryption, they begin to upgrade their connection.
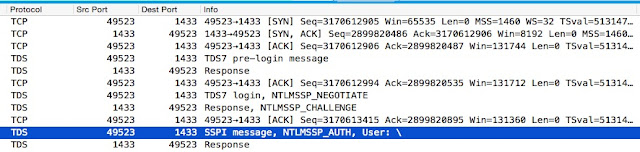
 |
| Initial packet capture: upgrading to encrypted connection begins after initial pre-login messages |
For our purposes, it would be better if
ENCRYPTION fields were set to
ENCRYPT_NOT_SUP(0x02), so that the server thinks the client doesn’t support encryption and vice versa. We hacked together a
crude TCP proxy to do this. We connect the client to the proxy, which in turn connects to the server and starts relaying data back and forth. The proxy watches for the specific string of bytes that mark the
ENCRYPTION field from either client or the server and changes it. All other traffic passes through unaltered.
 |
| Proxying the MSSQL authentication |
The proxy is built with Twisted which simplifies the connection setup. Twisted’s asynchronous/event-driven style of network programming makes it easy to match bytes in the traffic and flip a bit in the match before sending it along again. The match and replace takes place in the dataReceived methods which Twisted calls with data being sent in either direction.
With the proxy in place, both sides think the other doesn’t support encryption and the authentication continues in the clear.
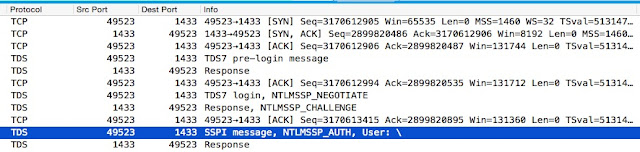
 |
| Traffic between the proxy and the server of an unencrypted authentication |
It’s to be expected that opportunistic encryption of a protocol can be stripped by a mitm. Projects like
tcpcrypt explicitly chose this tradeoff for interoperability with legacy implementations in hope of gaining widespread deployment of protection against passive eavesdropping. The reasons for Microsoft SQL authentication going this route isn’t spelled out, but it’s possible that interoperability with older implementations was a concern.
Related




1 comments On Stripping encryption from Microsoft SQL Server authentication
Thanks for sharing such type of information.