Attackers on your network love finding stray credentials. They are an easy way to elevate privileges and are often one of the first things attackers look for during post-exploitation. There’s no shortage of places where these credentials can be found and surprisingly, there’s very little downside to attackers trying them… …unless there’s a way to drop decoy credentials. This isn’t a new idea, but it usually requires heavy tooling and configuration. Our newest AD tokens allow you to create fake …
Year: 2023
Our Cloned Website Token has been available for a long time now, both on our public Canarytokens.org site as well as for our Canary customers. It’s helped users all over the world detect attacks early in the process. We wanted to take a moment and go over some of the details of this token: how it works, how to create and use one, and critically, how it fares against the new “Adversary-in-the-Middle” (AitM)-generation of phishing attacks.. The cloned website token …
Labs is the research arm of Thinkst but research has always been a key part of our company culture. All Thinksters are encouraged to work with Labs on longer term projects. These become that Thinkster’s “day job” for a while. (These are intended both for individual growth, and to stretch ourselves into new areas: They don’t have to be related to Canary or security). I took a brief hiatus from the engineering team to explore a computer vision project: CourtVision. …
Introduction We spend huge amounts of time sweating the details of our products. We want to remove all the friction we can from using them and want to make sure we never leave our users confused. To get this right, we do a bunch of things: we use simple language, we make extensive use of context-sensitive help and where it’s needed, we nudge users with illustrative examples. Recently we bumped into something that made us rethink our use of examples. Background …
Introduction Today we’re open-sourcing a research project from Labs, ZipPy, a very fast LLM text detection tool. Unless you’ve been living under a rock (without cellphone coverage), you’ve heard of how generative AI large language models (LLMs) are the “next big thing”. Hardly a day goes by without seeing a breathless article on how LLMs are either going to remake humanity, or bring upon its demise; this post is neither, while we think there are some neat applications for LLMs, …
This week we are super excited to release the latest addition to our lineup of Thinkst Canary platforms: Tailscale. Background We’ve always made sure that deploying Canaries is absurdly quick and painless. It’s why you can add a hardware Canary to your network just by plugging it in and why most customers end up re-thinking their detection roadmaps: https://twitter.com/bigendiansmalls/status/970342360923033601 We adore Tailscale: They have a first-rate team and their product is also widely loved for being startlingly simple to deploy. …
Introduction The AWS API key Canarytoken is a perennial favourite on Canarytokens.org, and we’ve heard requests for a similar token for Azure. In this blog post, we introduce the Azure Login Certificate Token (aka the Azure Token) to Canarytokens.org1. As with all tokens, you can sprinkle Azure tokens throughout your environment and receive high fidelity notifications whenever they’re used. Place one on your CTO’s laptop, or on every server in your fleet. When attackers breach that laptop, or servers, or …
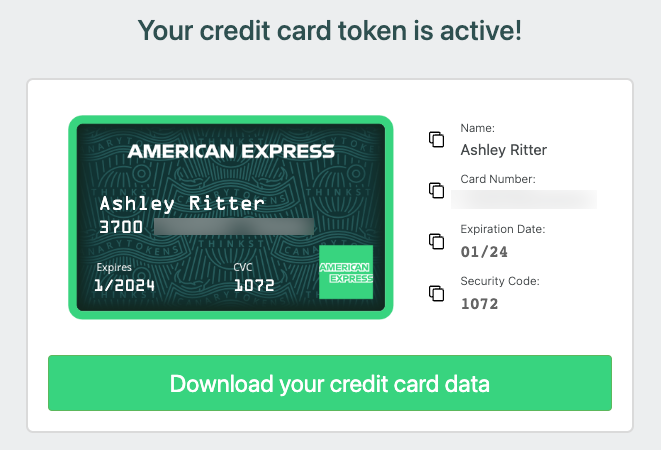
Detect breaches with Canary credit cards! TL;DR; Today we’re releasing a new Canarytoken type: actual credit cards! We recommend placing one anywhere you store payment information. If you ever get an alert on it, you know that that data-store has been compromised. Background Canaries generally aim to look like something an attacker would want to interact with. It’s why our mantra has always been that Canaries should look valuable (instead of just vulnerable). Historically, these have been network services, or …