Introduction
The AWS API key Canarytoken is a perennial favourite on Canarytokens.org, and we’ve heard requests for a similar token for Azure.
In this blog post, we introduce the Azure Login Certificate Token (aka the Azure Token) to Canarytokens.org1.
As with all tokens, you can sprinkle Azure tokens throughout your environment and receive high fidelity notifications whenever they’re used. Place one on your CTO’s laptop, or on every server in your fleet. When attackers breach that laptop, or servers, or machine, they’ll search for useful credentials and discover the Azure tokens. Such juicy credentials are too tempting to ignore, and when they try them, you’ll be alerted to the compromise.
Why is the Azure Login Certificate Token useful?
Azure is second largest provider of cloud infrastructure services in the world. Hundreds of thousands of organizations use Azure Cloud to run their infrastructure. Thanks to the growing Infrastructure as Code movement, many of them are bound to use programmatic command line access to manage their infrastructure.
Attackers know this too.
Searching for Azure credentials is almost standard post-exploitation behaviour and finding login certificates are an attacker’s dream. This token turns that around. One alert, when it matters.
Are Azure tokens just useful to Azure customers? Of course not; Canarytokens are useful across your actual vendor lines. You don’t need to be an AWS customer to deploy actionable and useful AWS API Key Canarytokens, and nor do you need to be an Azure customer to find Azure tokens useful at detecting compromises in your network.
Attackers who find them won’t decide not to use them because they really don’t think you are an Azure shop. They will lick their chops while testing access (and in doing so will tip their hands).
Creating Azure Login Certificate Token
It’s dead simple: head over to canarytokens.org, our public Canarytokens service:
- Select ‘Azure Login Certificate’ from the drop down list.

- Enter an email and a token reminder. We use the email address to notify you when the token is tripped. The reminder you choose will be attached to the alert. (Choose a unique reminder! Nothing sucks more than knowing a token is tripped, but being unsure where you left it). A good Reminder is something like “Azure Token deployed to c:\Users\Administrator\ on DC-LON-02”, which clearly highlights where you placed it.
- Click on “Create my Canarytoken”:
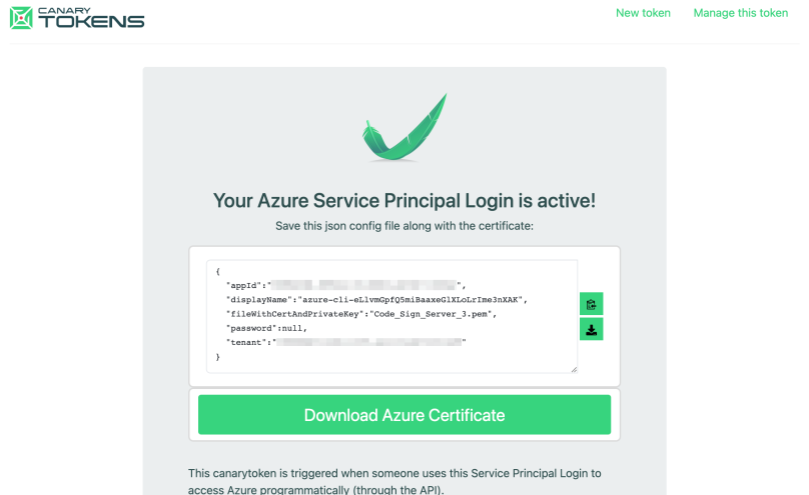
- Congratulations, your new Azure token is ready to be deployed! The output displayed can either be copied into a new file in the place you want to deploy the token, or you can download a file and move it into place. Don’t forget to delete an intermediate copies of the data.
Testing the Azure token
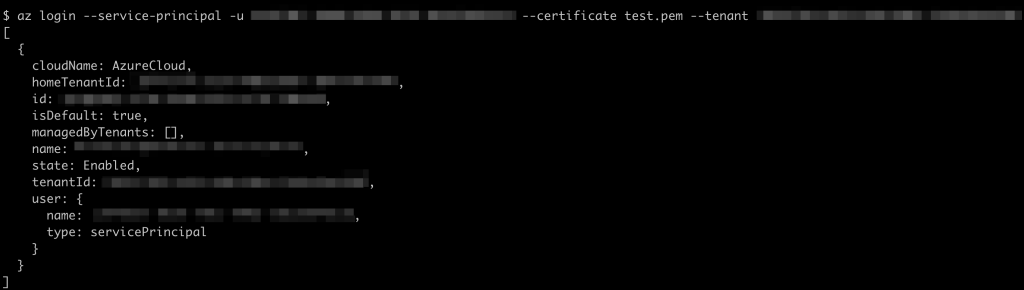
On Linux (with the az tool installed), the token can be triggered simply by running:
$ az login --service-principal -u <app-id> --certificate <certificate> --tenant <tenant>with the relevant parameters updated using the information from the token. As an example:
Within 5 to 10 minutes you’ll get an alert notification indicating that the credentials have been used:

Where to deploy the Azure Token
Place the Azure token config file alongside the certificate in a juicy place for potential attackers to find.
Most systems have a ~/.azure folder (much like the ~/.aws or ~/.ssh) and you can place the config file and certificate there.
Behind the scenes
The route followed is similar to what we do with AWS Key Canarytokens. In short, we pre-generate credentials programmatically into a pool of available credentials because each takes a few seconds to create. These are later allocated to a user when they request a new Azure Canarytoken. We then monitor the usage logs of the Azure accounts in which the credentials were created, and if credentials were used we send the alert.
Wrapping up
The new Azure Canarytoken gives Azure customers (and everyone else) a simple new way to detect breaches, by deploying Azure credentials at no risk to themselves in places attackers would typically find them.
Azure tokens are currently live on Canarytokens.org, and (as always) are completely free.
They take just minutes to create and deploy (even if you are a slow typist). Try them. They are totally worth the time.
Footnotes
1Commercial customers have had this token for a little while now.
