Would you know if your phone was hacked? Even the most powerful people in the world (if you use wealth as a proxy for power) don’t.
The problem is that much like your networks there are an almost unlimited number of ways for attackers to break into them, so this problem seems intractable at first blush. But (just like when they break into your networks) attackers who break into your phones are looking to achieve certain objectives, and you can use these objectives to reliably detect them.
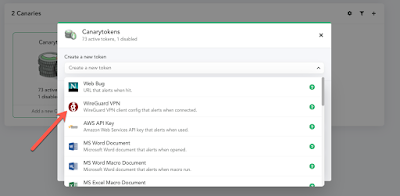
Today we released our new version of Canary, and with it, customers also get the shiny new WireGuard Canarytoken appearing on their consoles.
What’s a WireGuard?
WireGuard is the incredible VPN built by Jason Donenfeld. We love it. We use it. People smarter than us think you should too.
What’s a WireGuard Canarytoken?
Once a serious attacker gets onto your device, they have a certain set of objectives.
- Grab salacious data;
- Grab access to other services;
- Ensure repeat access or spread their compromise further.
In general, Canarytokens are little tripwires that you can place on your devices or in your applications which reliably let you know when they are accessed. Canary customers are able to deploy an unlimited number of these tokens around their networks and non-Canary customers can get the same benefit by visiting our free hosted server at canarytokens.org.
So, the WireGuard token looks like a regular WireGuard VPN connection on your device.
To deploy a Wireguard Canarytoken to your CEO’s or CFO’s phone, simply download the setup from your Canary Console (in a handy QR-code if you like), and configure the VPN on their device. (In fact, you should probably drop some on key servers too). And then… forget about it!
When the sort of attacker you care about compromises that phone (or that device), they see a VPN and can’t resist checking what’s on the other side of it. And as soon as they do, you’ll get a notification saying someone tried to connect to that VPN (and it’ll identify whose phone it was).
Setting up the token is dead simple:
1) Select the token from your Canary console;
2) Give the token a friendly reminder;
3) Use the WireGuard app to snap the generated QR Code.
4) That’s it.
So when you notice that your CEO is still in Seattle, but his VPN was just accessed from Saudi Arabia… that’s a raging clue.
We love Canarytokens like the WireGuard token because even if the attacker suspects that it’s a trap, it’s really hard to avoid using it.
What do you do as an attacker? Simply ignore the potential access it might yield? (You could, but that’s going to slow you down terribly, which would be a win for team defense too).
The WireGuard Canarytoken is available on all Canary servers today and will make its way to the public Canarytoken server in the next few weeks (when we will explain more of its inner workings).








5 comments On Would you know if your phone was hacked?
Hah! Such a great find! Please DM @thinkstcanary (or drop us an email) so we can send you some Canary gear to say thanks (for the spot!).
Your qrcode for the wireguard enrollment isn't obfuscated enough to break the error correction offered by the particular qr code 🙂
.
We have a pretty simple/straight forward one. Please drop us a note at sales@canary.tools and we will make it happen.
Do you have a reseller program?