Adversaries love (ab)using security software – why wouldn’t they?
Security software as a target
Security tooling is widely deployed, typically controllable remotely, and usually runs with elevated privs. This makes attackers greedy for credentials to security back-ends, and we can exploit that greed! In this post we introduce our latest Canarytoken: the CrowdStrike API Key

Adversaries are always on the lookout for credentials, and by placing decoy keys in their path it’s possible to detect them early.
They love API credentials because they have goals & objectives, and more often than not, API keys provide them with healthy in-roads towards them..
Crowdstrike RTR
Security tooling is infamous for being the shadow keys to the kingdom. If we take a look at CrowdStrike’s Real Time Response (a feature of their EDR), it’s a great example of why. RTR is essentially an online remote shell on every endpoint with Crowdstrike installed. With the right access RTR can give an operator the primitives they need to do real work across an environment.

Attackers know it too, and that’s why those credentials are valuable during hacking operations.
Crowdstrike API Key Canarytoken
Our new Canarytoken lets you generate a valid CrowdStrike client credential in seconds. You then deploy it wherever “helpful creds” tend to accumulate. This could be on security analyst endpoints, in scripts, in config directories(in those folders everyone says they’ll come back to clean).
When an adversary runs into those credentials they almost have to use them. And when they do, they end up exposing themselves..
How to Create them? Dead Simple:
- Visit Canarytokens.org and select the Crowstrike API Token;
- Enter an email address (to receive your notification) and a brief memo to remind you where you are placing this key
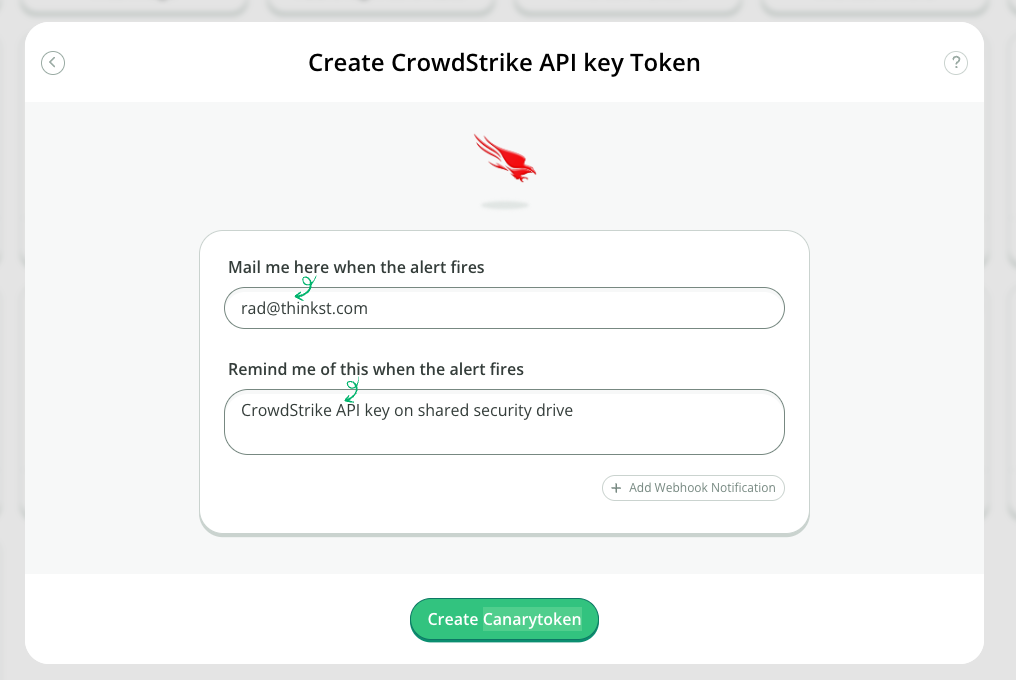
- And that’s it!
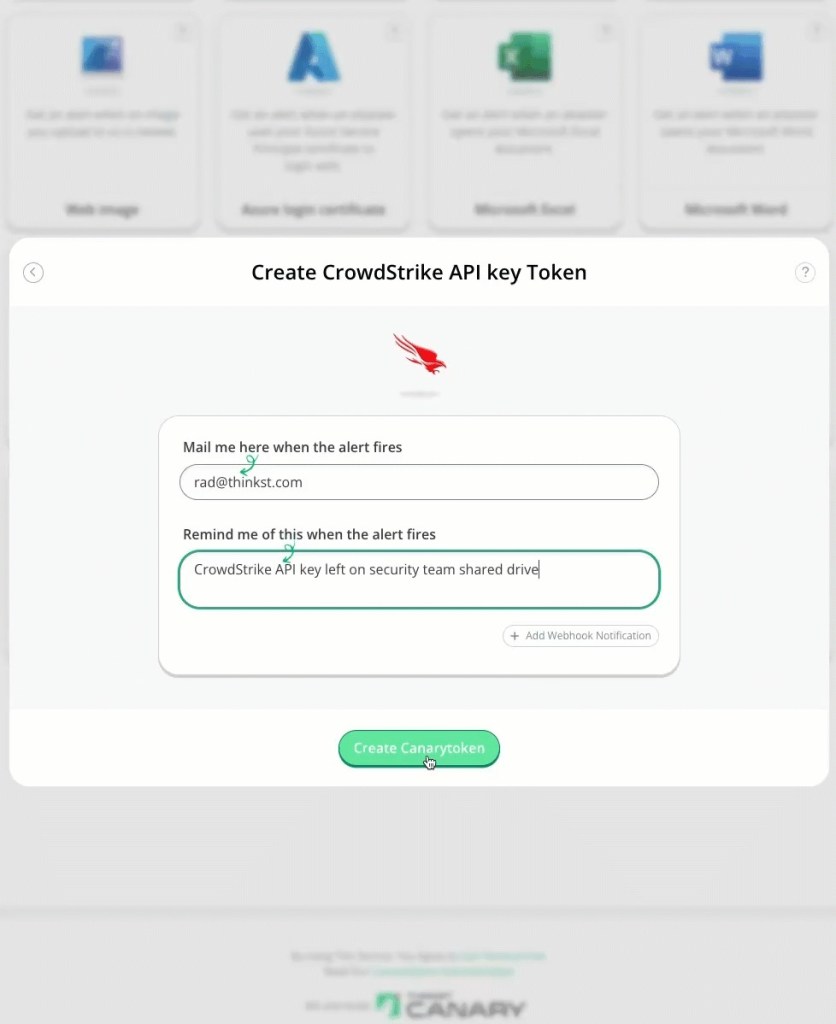
Place your token in a single location where attackers will find them and wait..
Internals
We create the credential in our own sandboxed tenant (so nothing of yours is ever exposed) and we obtain authentication notifications through CrowdStrikes excellent audit logs (Kudos to CS for being a rare security vendor who makes these easy to consume).
This is important so we’ll repeat it: there is no risk to your Crowdstrike tenant as everything lives inside ours. (You don’t even have to be running CrowdStrike in your environment, but your attackers won’t know that). Simply copy a few lines of a text file into a single location in your environment, to get the benefit.
Attackers can’t tell the difference, and you obtain that one high fidelity alert, when it matters.
Wrapping up
Give attackers options. Make them pay. The new Crowdstrike API Key Canarytoken is live and ready for you to try out and deploy.
Generate one here: https://canarytokens.org/
References:
https://attack.mitre.org/techniques/T1219
https://securelist.com/miner-campaign-misuses-open-source-siem-agent/114022
https://cloud.google.com/blog/topics/threat-intelligence/unc3944-targets-saas-applications
