(This Post was written for ITWeb for the Upcoming ITWeb Security Conference)
A security guy talking about impending doom. How rare! Except I’m not talking about the next Botnet, virus or nuclear reactor destroying worm, I’m talking about the crisis of confidence that’s heading our way, and the fact that we seem completely oblivious to its arrival. We (in the field) have been building a house of cards, and some day really soon it’s going to come down around us.
10 years ago, the Infosec industry was in its infancy and we complained bitterly about the lack of management buy-in while we struggled to justify our existence in the corporate hierarchy.
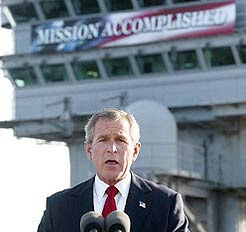
In the mid 90’s we started getting taken seriously. Firewalls and security policies became a part of the corporate lexicon and security teams grew in size. For a while it seemed like the game had equalized, our efforts matched the threats of the day, but the threats of the day were pranksters and kids. We cried “Mission Accomplished” too early.
The threats evolved and the attackers became professionals while we started getting used to corporate meetings, Aeron chairs and TPS reports.
We kept whining though. We need more budget! Management don’t buy in! We were actually compiling our list of excuses for our complete and utter failure to achieve our objectives, and we have failed! Think it’s not that bad? Here’s a simple, sobering hypothetical I posed in a talk last year: imagine the highest value individual at your corporation. The guy who’s computer (and the data assets it touches) you would do anything to protect. Can you honestly say you can stop a determined attacker from compromising him?
For the thousands your organization spends on security, you can’t protect the one guy who is most valuable to you. Worse yet, would you even know if he was popped?
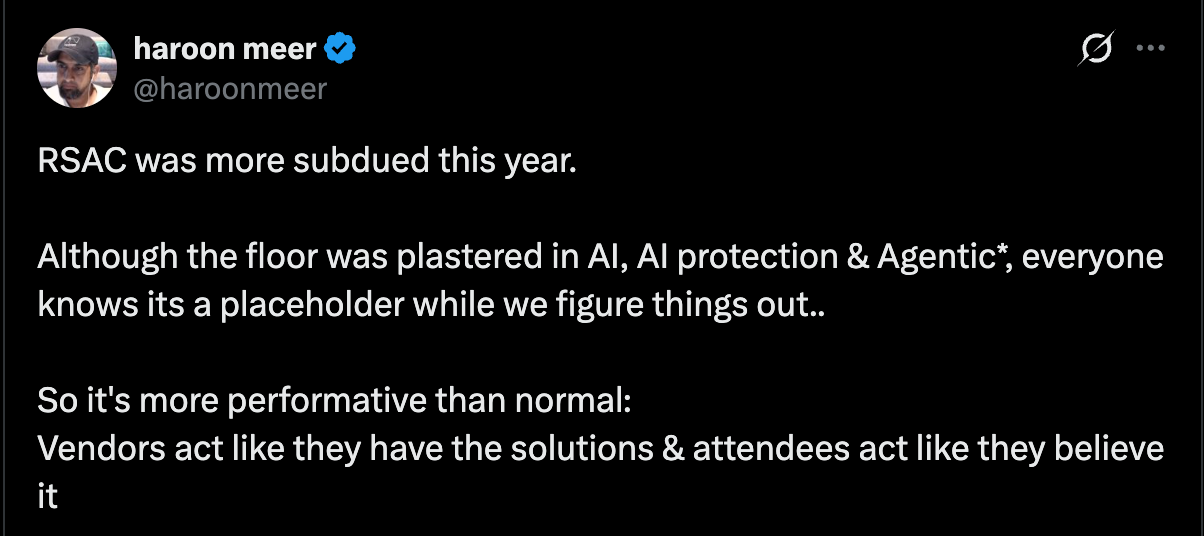
How ineffectual can we be? This problem compounds, because the company boards are now increasingly aware of the Infosec problem, but they are making the logical assumption that the teams of people they are paying, have the problem under control. They don’t know that we don’t have the answers yet, that many of us are resorting to hope as a strategy, hoping desperately that when the breach eventually happens, it won’t happen on our watch.
We find ourselves now in a strange position. The boards pay our (sometimes huge) salaries and send us to conferences and even though we occasionally whine, they assume we have the matter in hand. They think the millions of dollars being spent worldwide on penetration tests and anti-virus means that we could at least protect the CFO. We know we can’t but somehow, just never find the right opportunity to let them know.
The industry itself has become so incestuous, that we strongly resemble the investment banks just before the melt-down. Lots of money changing hands. Surface level checks and balances being executed by people with a strong disincentive to speak truth to power. Everything will hum along, until it won’t!
Everyday that we do not suffer the critical attack of our nightmares, is an additional day that makes people think the attack is less likely. As Taleb points the scarcity of the Black Swan event does not alter the likelihood of it happening, it merely makes the result more shocking when it does.
The board is going to be asking: “Isn’t that what we paid you guys to prevent?”.
There’s going to be some feet shuffling, some finger pointing, and some heads will roll.. honestly, I think we are going to deserve it!

4 comments On Our Upcoming Security Apocalypse!
This comment has been removed by a blog administrator.
Haroon: I agree. The security industry, in general, has been selling snake-oil solutions (anti-virus leaps immediately to mind…) rather than permanent (and workable) fixes. There's an immense amount of discussion about “best practice” and “compliance” at conferences, but very little discussion about Making Security Happen. Part of the problem, as I see it, is that the latter discussion needs to involve a heart-to-heart conversation about trust and privacy and values and compromise … but that's so-difficult, and we slap Process and Procedure and Method onto the problem instead, and pretend that they're acceptable substitutes. Security is a human thing, and the industry treats it as a technological issue; until that mindset changes, I'm not holding out for real progress.Pieter: you're conflating risk management and security. The former is necessary, but not sufficient, for the latter. I think you might have a bit of “lack of the big picture” there ;).Rob: (1) and that challenge needs to be meaningfully regarded and responded to, rather than being brushed off by organisational security custodians with “we're following Best Practice, so get lost”. Agree with (2) … but the devil's in the details, and the detail here is the word “independent”.
Thought provoking. My possibly contentious response:1) InfoSec activities and functions need to become more visible and tangible (as you say) so they can be challenged2) Independent assurance providers have a crucial role to play in a) validating the control environment is operating as everyone believes (and that it is protecting the right assets) and b) speaking up when this isn’t the caseI would be a little less worried once we get back to doing what we’re supposed to be doing which is securing information in its various forms and step out of the complex technology world we’ve created. The simplest forms of attack are still often the most effective.
Good post as always Haroon, but I have to differ. As you well know, I work for a corporate, small little place that sells bake beans. In the bigger picture, info-sec is all about risk management. I'm going to use one of the compliance issues as an example. As a retailer, PCI-DSS hits us right in the face. When we elevated the need for compliance to the board, one of their first reactions was “how much is the fine for non-compliance?” It's a valid question. If spending millions on compliance every year is more than the fine, why spend it.Only when the risk of transaction switching not happening was highlighted (and for a retailer the ability to accept plastic is slightly important), did the board agree that spending money towards compliance was worth the risk.The biggest fault I see in security professionals today is a complete lack of big picture. Some are worried about privacy, some about certification, and others about the raw code of the latest Android / Apple exploit. Your CEO, the one you want to protect, does not care about this. If he has to break the rules in order to load the newest SAP Gui on his iPad, then so be it.The biggest favour security professionals can do to the business is not getting a ticket to Vegas or Brussels, it's spending 10 minutes with your BA or BPO and understanding the risk in your business, and putting measures in place to manage that. Myself, I would love to try break something. Unfortunately I am dealing with a 200 page audit report that highlights the risks we face, I have to prioritize them and make sure they are mitigated within a time frame. The board knows there are risks, but they know there's also only so much money that can be sent my way to stop the risks, and that's how I see them managing the risk.