Introduction:
Many people have pointed out that there are a handful of commands that are overwhelmingly run by attackers on compromised hosts (and seldom ever by regular users/usage). Reliably alerting when a user on your code-sign server runs whoami.exe/klist.exe/nltest.exe/etc. can mean the difference between catching a compromise in week-1 (before the attackers dig in) and learning about the attack on CNN.
Introducing our new Sensitive Command Canarytoken.
This quick/simple Canarytoken alerts you any time your chosen command is executed on a host.
For example: This token creates registry keys to alert you anytime klist.exe runs on a host.
If an attacker lands on the server and runs klist.exe (as most attackers almost instinctively do) they get the results they expect.
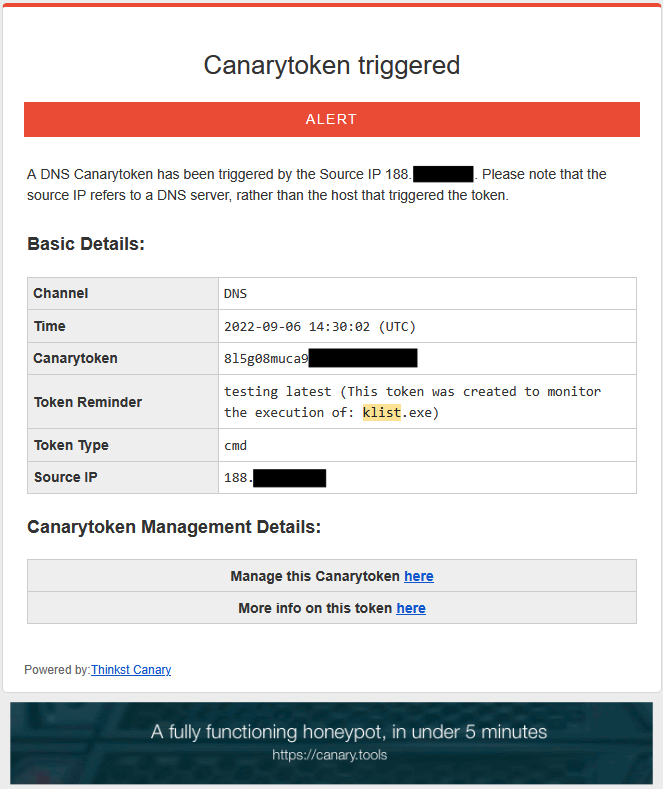
And you get an alert to let you know that something bad is afoot.
Why this token?
In nearly every ransomware report, we can see attackers running a series of predictable commands on endpoints.

Some of those commands are almost never run by regular users through regular usage. This means that they become high quality markers of “badness”.
Wouldn’t it be great to get an alert the moment someone runs WMIC on your code-signing server? Or the moment someone runs whoami.exe on your SQL-Server? Many organizations will use EDR (Endpoint Detection and Response) tools to do this. However these complex telemetry streams, and detection logic may not be available to small organizations, may not be comprehensively deployed and often require specific configuration changes to alert on these invocations.
We want to know, and we want the setup to be dead-simple.
tl;dr – Just show me the token
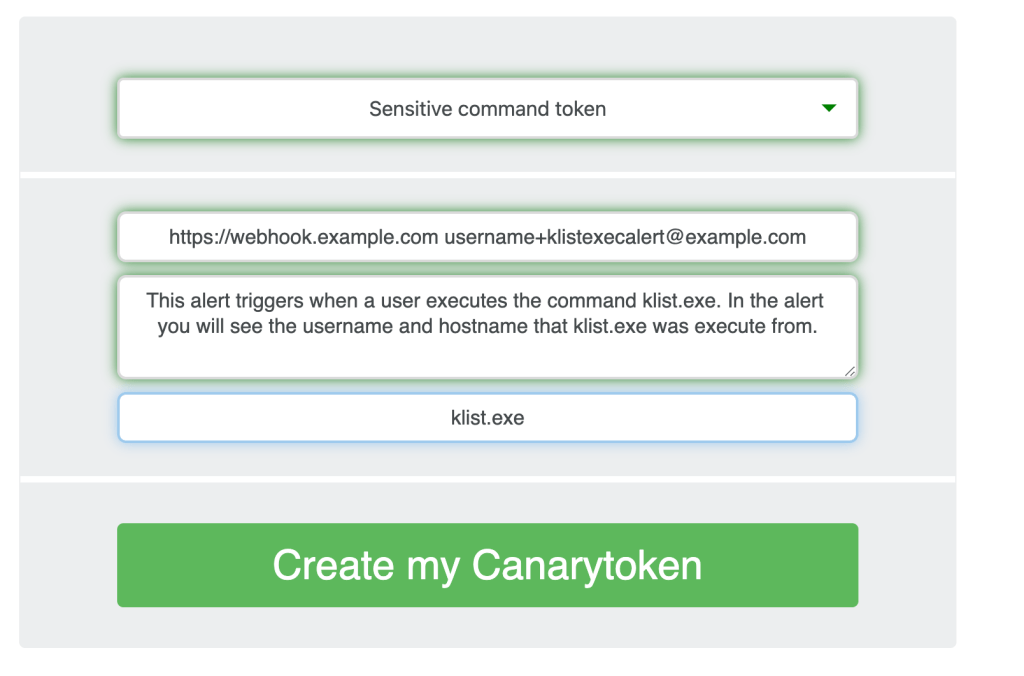
If you visit https://canarytokens.org and view the list of available tokens, you will notice a new Canarytoken type: “Sensitive command token”
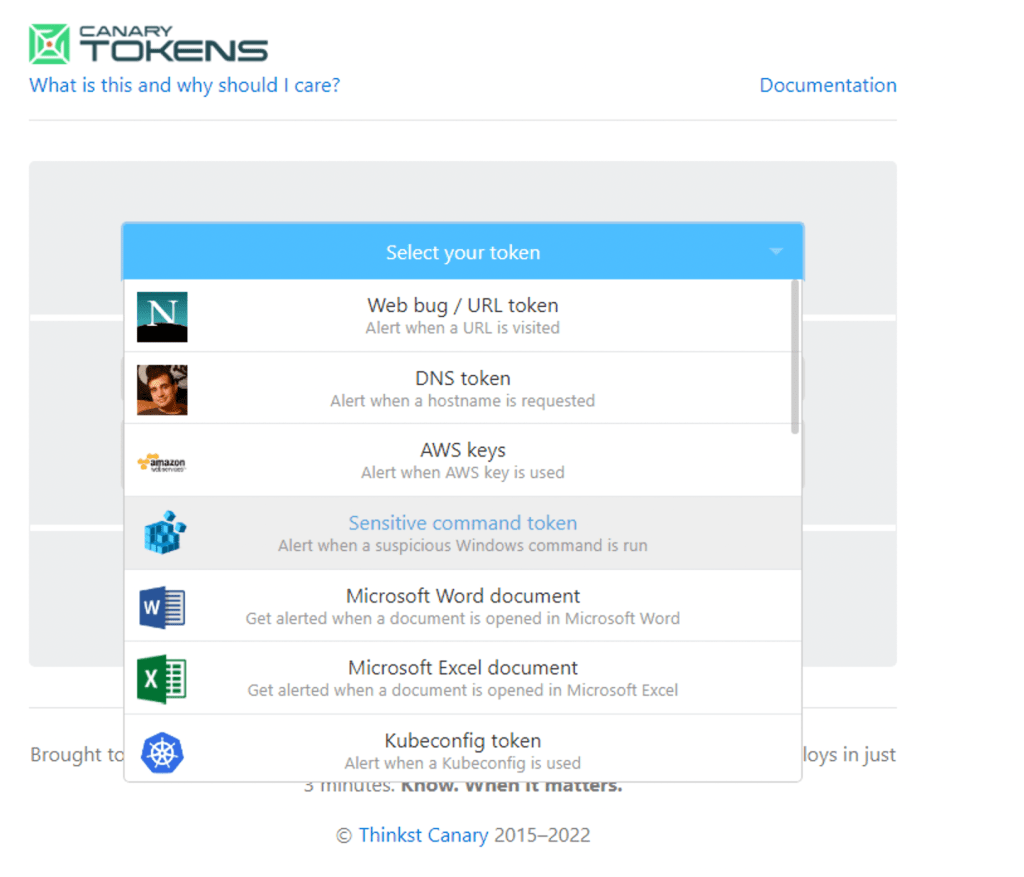
Choose the Sensitive command token.
Next, like other Canarytoken configurations, we add some quick details:
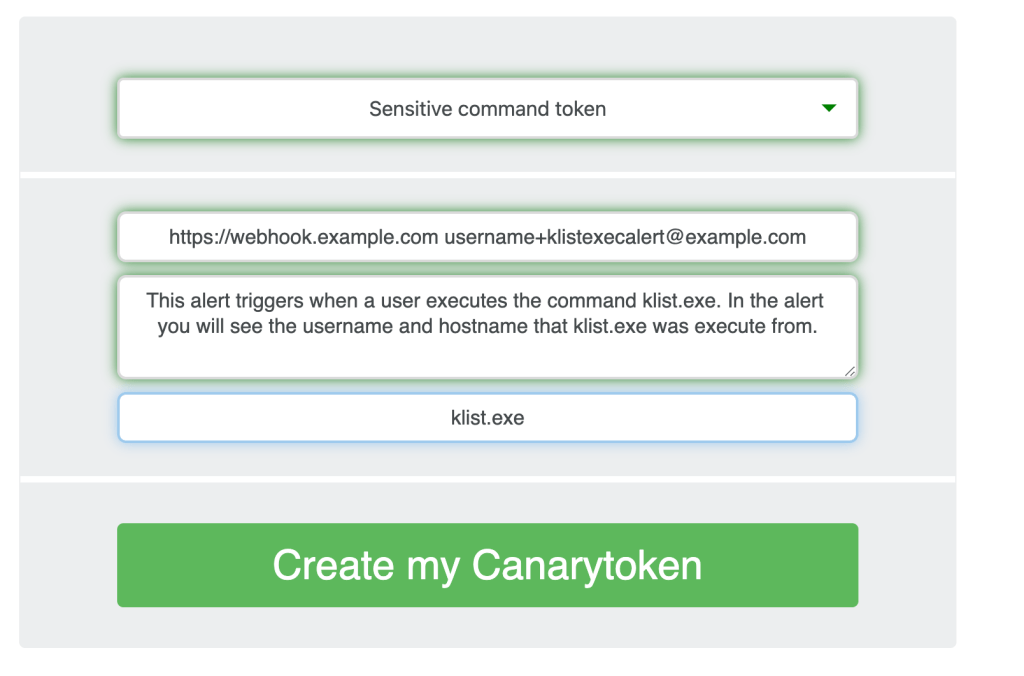
[1] Where to send the alert, (email or webhook, or both);
[2] A reminder note, that will help you react when you receive an alert from this token;
[3] Choose the process that you want to monitor execution for (e.g., wmic.exe, whoami.exe, klist.exe, nltest.exe).
The Canarytoken server will create a .reg file for you to download and import onto a Windows 10, or Windows 11 system (or use GPO to deploy across multiple systems).
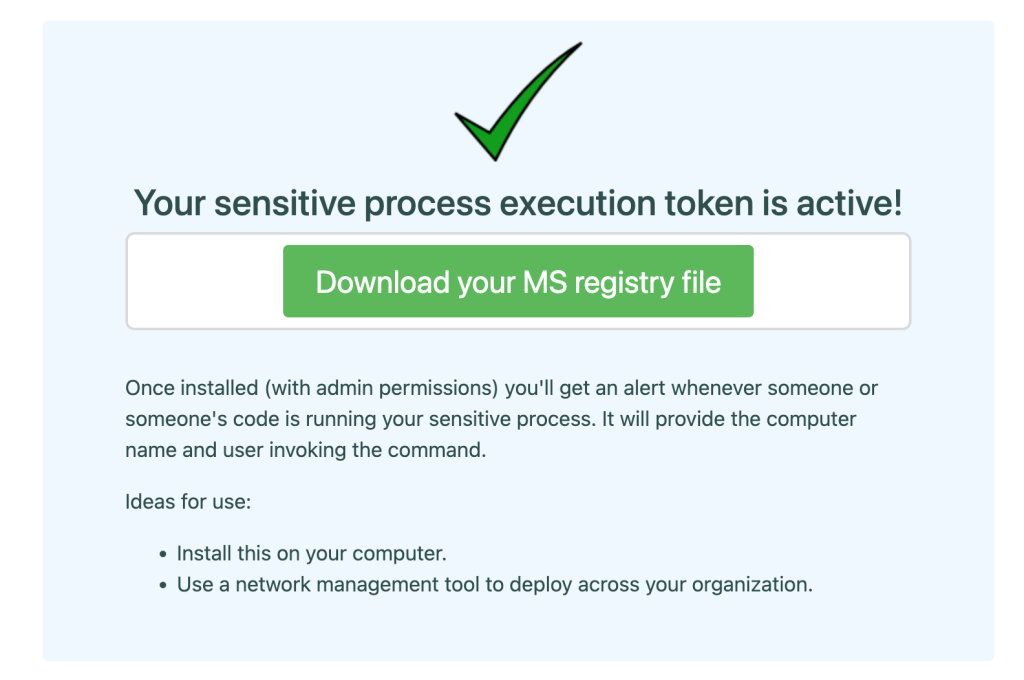
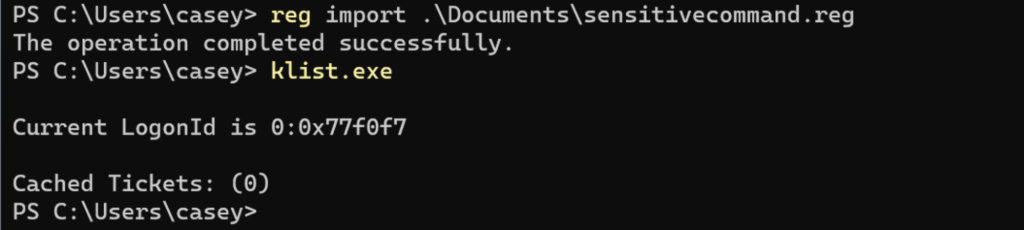
Once you have downloaded the .reg file, you can import this to the system (or systems) you want to monitor.
reg import
Remember this will require local Administrator permissions.
That’s it! If a user on this host ever runs that (sensitive) command, you will receive an alert!
It’s worth noting that this Canarytoken does not impede or alter the original command in any way, it simply sends you a near real-time alert that someone has executed our tripwire.
In the alert you will see the details of the time of the alert, the user that executed the command, and the computer name the command was executed from.

Note:
A subtle benefit of how this token is designed allows you to deploy the same token on multiple machines without making any changes. Running reg import across a host of machines will tripwire them all, and when an attacker runs her command on any one of them, you will know.
There you go!
We can now create a Canarytoken to alert us on Sensitive Commands that execute.
These commands may be sensitive due to the fact that they are rare, used by attackers, or are sensitive to your organization. How you choose to pick the executable is up to you.
Bonus: the executable does not need to be present on the system. Suppose your organization never uses adfind.exe. You could add this tripwire, so that if someone ever downloaded that to your system and executed it you would be notified.
Additionally you sometimes don’t want to run AV/EDR on some machines, or 3rd party systems that won’t allow you to install software, but here you can monitor an executable or five.
That is all you need to get started using this new Canarytoken. If you would like to learn more about the architecture and mechanics under the hood: continue reading.
Under the hood
Problem Statement:
We wanted to see if we could find a way to generate an alert to our console when a suspicious command is executed on a system. Without interfering with the original command execution.
The best candidate command for this alert is one that is rare, short lived, and used by attackers.
In short, if you want to receive an alert if someone runs wmic.exe on a workstation, this may be the Canarytoken for you. This token creates a .reg file with three registry entries that you can import to the system. You will need Windows 10 or 11, and Administrator access to the systems you want to add this to.
Token Architecture:
Our team spent a number of cycles trying various experiments and approaches to generating an alert based on process execution. From doskey, to wmi, to performance monitoring. We settled on an older Pentesting Persistence trick that in the end met all our requirements.
In his blog post on “PERSISTENCE USING GLOBALFLAGS IN IMAGE FILE EXECUTION OPTIONS“, Oddvar details how to persist in the registry and execute a command on a Windows system that runs in the background. This technique meets our requirements exactly. We needed a tripwire that would run in the background, not interfere with the original process, and allow us to make a custom callback/alert over DNS to alert a system administrator, or security team, that a suspicious command had been executed on the system.
(We have also seen a debugger variation of this technique used by high profile attacks as well.)
“The attackers achieved this by having the SolarWinds process create an Image File Execution Options”
We will repurpose the mechanics of this attacker technique and turn it into a defender tripwire!
Oddvar demonstrated his technique to establish persistence and run an arbitrary executable, we will use it to reliably generate a remote alert.
This Canarytoken does not add any new executable to your system thanks to the wonders of Oddvar’s technique, built-in tools and the Canarytoken server. We will be using Microsoft’s built-in SilentProcessExit monitoring, documented here:

The specific registry settings we are interested in:
Image File Execution Options\{ProcessName}
SilentProcessExit\
MonitorProcess
ReportingMode
You will see in the registry output above, we set this to the value 0x200. You may need to ensure that the process you wish to monitor isn’t impacted by this setting.
Next we set the ReportingMode to 0x1.
“When silent exit is detected, the monitor process (specified in the Monitor Process box) is launched.”
The bulk of the work for this alert is what we configure in the MonitorProcess value.
Let’s break down the command to trigger this alert:
""MonitorProcess"="cmd.exe /c start /min powershell.exe -windowstyle hidden -command \"$($u=$(\\\"u$env:username\\\" -replace('[^\\x00-\\x7f]|\\s', ''))[0..63] -join '';$c=$(\\\"c$env:computername\\\" -replace('[^\\x00-\\x7f]|\\s', ''));Resolve-DnsName -Name \\\"$c.UN.$u.CMD.g6jjwnaukbfddgz51kh8tacdc.canarytokens.com\\\")\""
The various \\\ sequences are to ensure proper escaping for both the command to run and to import into the registry.
First we call “cmd.exe /c start /min”. We do this as a trick to make the execution of our alert appear to run in the background. Even when we set -windowstyle hidden, with PowerShell, a window would appear, briefly but this wasn’t acceptable to our goals. We also added some code to remove the non-unicode characters and to remove spaces. To ensure the alert data can be passed over a DNS query.
Next we run a PowerShell command to resolve our Canarytoken DNS.
We can leverage our ability to encode data into the DNS request. This is documented here
Our lookup captures computername.username.token. Why PowerShell? We had some interesting collisions with trying to use the %computername% environment variable in say an nslookup command, due to the fact that MonitorProcess parses the registry key and uses the %c to report a status code. So after a few iterations, and experiment we found PowerShell the easiest way to collect the variables we need and add them into the alert.
Risks/challenges/considerations.
- Installing the .reg file requires admin privileges;
- Selecting the wrong “sensitive executable” will yield false-positive alerts;
- Hostname and Username are sent in clear-text in the alert;
- Process level alert: we only see that the process was executed, this approach does not give us command line granularity;
- These commands may, upon installation, look like attacker commands . Not the alert itself, but the installation, this is due to the fact we are repurposing an attacker trick;
- This alerts on all executable matches for the filename. If you need further refinement, you can customize this by setting the FilterFullPath registry key;
- Image Architecture, these keys were tested for x64. You may need to customize the settings if you are hoping to alert on x86/32 bit execution. C:\Windows\SysWOW64\whoami.exe may evade the alert. Again, something to be aware of if you are looking into these for critical areas;
- This alert won’t catch a renamed binary since the alert triggers on the process name.
For example, our Canarytoken alert won’t fire if the binary has been renamed, but that is ok. If you need a tool that alerts on Process Execution, by OriginalFilename, Location and Command Lines, there are several to choose from. We just wanted to call that out, so you are aware of some of the limitations of these types of alerts.
We do also see utility for teams to set tripwires for executables they never wish to see executing. Suppose we want to set a tripwire for mimikatz.exe. We can create the registry key, even though mimikatz.exe is not present on the system. Then if anyone ever executes a file with that name, we will receive an alert! You may also extend this to internal tools or executables as well.
Choosing a binary to monitor:
Candidate sensitive commands:
- Short lived, exits quickly
- Low frequency
- Low execution prevalence
- Indicative of suspicious or unusual activity.
Each organization will need to look at command frequency, look into various threat reports and make that decision. If you need to disable a Canarytoken like this, you could for example set the Image File Execution Options \GlobalFlags value to 0x0, then set it back to 0x200 if need be.
For example: We’ve seen in nearly all ransomware attacks, schtasks.exe be leveraged. This binary at first blush seems like the ideal candidate to token but it turns out that schtasks runs frequently in the background, so it doesn’t meet the candidate criteria of Low frequency.
Additionally Windows will create an event in the Application log when these events occur. These may allow teams further investigation data. The only requirement to record these events is that the Image File Execution Options\{ProcessName}\ GlobalFlags key be set to 0x200.
For those interested in additional details, you will also see the EventID 3000 in the Windows EventLogs to indicate Process Exit Monitor has occurred. Teams that are interested in a lightweight process monitoring record. Can simply create and set a GlobalFlags == 0x200 , and they can observe over time whether or not the process is frequent or not. Also they can determine if the process runs and ends quickly. This may also be a good Indicator of Compromise , for teams not expecting to see a particular process with this flag set.
As an example you can see below a quick way to search for these events and extract the Usernames.
$Events = Get-EventLog -LogName Application -InstanceId 3000 -Source "Microsoft-Windows-ProcessExitMonitor"
$Events | %{ $_.Username }
Conclusion:
We looked at creating a new Canarytoken type that allows us to receive an alert when we specify an executable name that we want to watch for. We can do this by adding three registry keys and a PowerShell command to trigger a DNS lookup for us. We overload the DNS request with sufficient data to generate a meaningful alert for defenders. (We wrap all of this up in one simple .reg file import).
We discussed some of the advantages and disadvantages of this approach. We are able to do this by leveraging the alert pipeline that you have, perhaps already used. If you would like to customize these tokens you certainly can too (and you can always run your own custom version of the free Canarytoken server. See the GitHub repo here https://github.com/thinkst/canarytokens).
Thank you for taking the time to read, and we welcome feedback on ways to improve and refine this new Sensitive command Canarytoken. Thanks again to the Applied Research team at Thinkst for all the testing and feedback to help us bring an idea forward that may prove helpful.
References
- https://thedfirreport.com/
- https://oddvar.moe/2018/04/10/persistence-using-globalflags-in-image-file-execution-options-hidden-from-autoruns-exe/
- https://www.hexacorn.com/blog/2019/09/19/silentprocessexit-quick-look-under-the-hood/
- https://scorpiosoftware.net/2018/09/21/silent-process-exit-is-it-really/
- https://docs.canarytokens.org/guide/dns-token.html#what-is-a-dns-token
- https://www.geoffchappell.com/studies/windows/win32/ntdll/api/rtl/rtlexec/openimagefileoptionskey.htm
- https://attack.mitre.org/techniques/T1546/012/
- https://github.com/BishopFox/sliver/wiki/DNS-C2
- https://unit42.paloaltonetworks.com/more-xhunt-new-powershell-backdoor-blocked-through-dns-tunnel-detection/



8 comments On Sensitive Command Token – So much offense in my defense
Are Sensitive Command Canarytokens limited to interactive / GUI sessions? When accessing a server with Enter-PSSession, running “whoami.exe” won’t trigger the (otherwise working) canarytoken.
How bout the option to remove from the registry?
Pingback: Monitoring Sensitive Windows Commands via CanaryTokens - Deploying Registry Entries via Group Policy | Cyber Elias Tube ()
Would it be possible to add and “Ignore List” similar to what exists for the Cloned Website Token that could operate against the User or Computer fields? I can already see where some of the commands that would be good to monitor are being executed in my environment due to legitimate background processes which will cause unnecessary noise.
This looks awesome, I will test this definitely.
It is a great question. This approach as we designed it, is really process specific.If you needed to get command line, you could certainly customize the token, perhaps prefix it with logic to check the command line. However this isn't part of the default token build.For example :Insert Get-WmiObject win32_process -Filter 'ProcessID = %e' | select CommandLine Where %e, is the ProcessID of, the process you are monitoring.However, you can likely do this easier with more complete command line monitoring tools.Hope that helps.
We can easily monitor “net.exe” – but can we specifically alert on commands i.e. '”net localgroup administrators” ?
Great