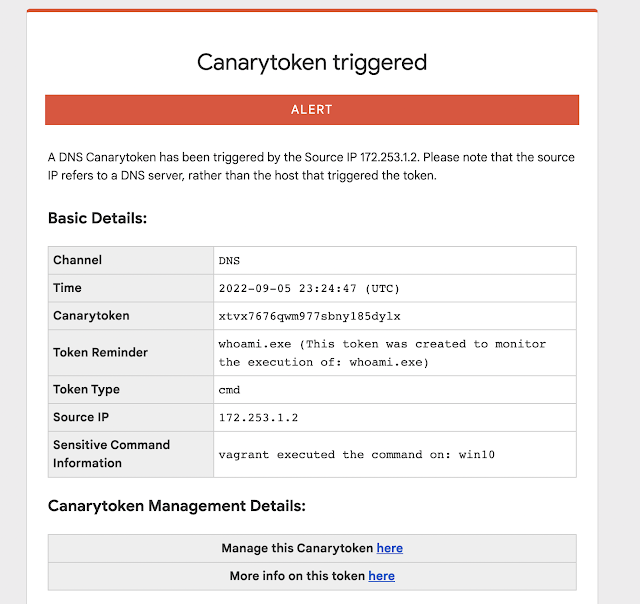
Introduction: Many people have pointed out that there are a handful of commands that are overwhelmingly run by attackers on compromised hosts (and seldom ever by regular users/usage). Reliably alerting when a user on your code-sign server runs whoami.exe/klist.exe/nltest.exe/etc. can mean the difference between catching a compromise in week-1 (before the attackers dig in) and learning about the attack on CNN. Introducing our new Sensitive Command Canarytoken. This quick/simple Canarytoken alerts you any time your chosen command is executed on …
Blog Posts
Introduction This post is the first in a series by Canary customers where they detail how they integrated Canaries and Canarytokens into their security practice. This series hopes to showcase how organizations of varying sizes and structures deployed and acted on alerts to improve the security of their networks. Casey Smith recently joined Thinkst Labs, today he’s sharing his experiences with Canaries and Canarytokens from his previous role as a customer. Background Prior to joining Thinkst, I worked for a …
We discussed this Scott Forstall clip internally and figured it was worth sharing since theres so much going on in just 5 minutes. Bradley commented on how familiar it felt to how we roll and it’s worth digging in to this little more. Quick Background In 2007 Apple was not yet a trillion dollar company, but its star was definitely on the rise. Jobs was back, OSX was taking root and the iPod was game changer. (Their market cap was …
Given the importance of REST API endpoints for most networks and applications, we wanted a way to use (existing) Canarytokens, or Canaries to detect unauthorized access to a REST API. (Like all things Canary) We wanted something easy to use that delivers immediate value. Here we present several new approaches, and look forward to hearing from the community on the usefulness and ways to increase insight here for network defenders. Challenge: APIs are everywhere and permeate most organization’s daily web …
The AWS API Key Canarytoken (paid and free) is a great way to detect attackers who have compromised your infrastructure. The full details are in a previous blogpost, but in short: You go to https://canarytokens.org and generate a set of valid AWS API credentials; Simply leave those in ~/.aws/config on a machine that’s important to you Done! If that machine is ever breached, the sort of attackers who keep you up at night will look for AWS API credentials, and …
To see a World in a Grain of Sand Rice – William Blake mh If you are on TikTok (or a fan of talk shows) at the moment then, no doubt, your feed has included coloured rice being tossed in the air in the form of song lyrics, beloved cartoon characters, and even famous faces. @mr.riceguy Whilst coloured rice is not a new thing (for most preschool teachers, it is a cheap and effective way to keep kids entertained), a bunch of …
Earlier this year we released our WireGuard Canarytoken. This allows you to add a “fake” wireguard VPN endpoint on your device in seconds. The idea is that if your device is compromised, a knowledgeable attacker is likely to enumerate VPN configurations and try connect to them. Our Canarytoken means that if this happens, you receive an alert. This can be useful at moments like national border crossings when devices can be seized and inspected out of sight. Using the WireGuard …
Introducing the new Kubeconfig Canarytoken A while back we asked: “What will an attacker do if they find an AWS API key on your server?” (We are pretty convinced they will try to use it, and when they do, you get a reliable message that badness is going on). Last month we asked: “What will an attacker do if they find a large MySQLDump file on your machine?” (We think there’s a good chance they will load it into a …
(The making of a MySQL Canarytoken) tl;dr Consider this scenario: An industrious attacker lands on one of your servers and finds a 5MB MySQL dump file (say, called prod_primary.dump). What do they do next? Typically, they would load this dump-file into a temporary database to rummage through the data. As soon as they do, you get an email/SMS/alert letting you know: Eds note: You can create and deploy these by visiting canarytokens.org (completely free; no registration needed) There are obvious benefits …
Last month Florian Roth (cyb3rops) reacted to the news of Mimikatz dumping RDP credentials by asking how we could easily inject fake credentials into machines. https://twitter.com/cyb3rops/status/1397440903476883458 Markus Neis pointed out that on Windows, cmdkey allows you to do this: https://twitter.com/markus_neis/status/1397472760859856897 This is pretty awesome. Mimikatz is used by attackers the world over and having control of the data a Mimikatzer will see is a powerful tool to have. One route to looking for Mimikatz usage is injecting false credentials into …